AN OVERVIEW ON
LOW-COST, SECURE WiFi MESHED NETWORKING SUITABLE FOR USE IN
DEVELOPING COUNTRIES, NATURAL DISASTER AREAS OR REMOTE COMMUNITIES
Introduction
-
At the core of NVTech is the desire to effect the rapid advancement of societies in developing countries, Cost-affordable Information and Computing Technology (ICT) is seen as being a potent enabler 1. The major components of ICT are seen as being:
-
Hardware. Over 200 million PCs are scrapped every year, often not because they are broken but because they can no longer satisfactorily run the latest version of Windows or related software, Hardware manufacturers may think that the provision of 2nd hand equipment to developing countries cuts into their own markets, It does not, Instead it develops markets and opportunities more quickly than would be the case if developing countries were deprived access to this “start-up” equipment. In some ways, low power machines are an advantage because usually in developing countries there is a shortage of electrical power, Solar charged mobile phones have been found in Bangladesh, for example, to be an effective means of delivering a wide range of services from banking to English tuition (sponsored by the BBC).
-
Software. Open Source Software is not only cost affordable, with packages such as the LibreOffice Suite, the Thunderbird and Evolution Email clients and the Mozilla and Chrome Web-browsers, it is of exceptional quality, In the case of Open Source Operating Systems such as Linux, there is the added benefit of being able to tweak the kernel such that the OS will provide acceptable performance on old machines.
-
Intranet and Internet Communications. Intranets and the Internet allow the sharing of information and the efficient conduct of commerce, The problem in establishing viable networks in developing countries is the lack of infrastructure both in terms of wiring and in electrical reticulation, Vandalism and pilfering can also be a problem.
The Role of WiFi
-
WiFi is a recent development in RF communications technology that may be useful in setting up low-cost, secure, metropolitan area networks, WiFi takes a different approach to utilising the available electromagnetic spectrum compared to conventional radio communications of the past, As at the time of writing it is possible to achieve a bandwidth of around 380 Megabits/second with a WiFi connection from a mobile computer to a single access point with an unlicensed transmitter having a range of around 500 to 750 metres, In a perfect world, this would be sufficient to support around 50,000 encrypted Voice over IP (VoIP) telephone calls; each requiring around 7 kilobits/second for a reasonable quality conversation, Alternatively, a high definition, 1080p, 60 frames per second compressed video stream will require around 20 Megabits/second. With a bandwidth of 380 Megabits/second, this allows for 19 such streams, However, the world is far from perfect. There are communications overheads and there is often interference, Nevertheless, WiFi has the capacity to deliver to the mobile device unprecedented quantities of digital signals and these may carry voice, video or data.
-
Secure WiFi networks can be produced and installed very cheaply; especially if one takes advantage of what is available from the Open Source Software community, The electronics contained in the example self-sustaining communications pole shown in Figure 5, for example, cost less than AUD$500.00.
-
"Extreme WiFi" network experimentation has been performed by NVTech and associates to explore the possibilities of using this technology. The results have exceeded expectations in terms of range, flexibility, survivability, reliability and low cost.
Potential Benefits
- The use of these WiFi networks is of particular interest because of their potential to provide secure voice and data communications for use by the government and business, These same networks would have sufficient capacity and security to allow their free use by private casual users, There is much benefit to be gained, at the strategic level, from the civilian population having unfettered access to information, These networks would also provide the ability for the people to conduct commerce and would facilitate the provision of law-enforcement, educational and health services, Achieving this increases significantly the chances of creating stability, employment and economic affluence which, in turn, will effect societal changes; all of which address the root causes of turmoil and political instability.
-
An essential element of this initiative is therefore not only to provide the very best level of connectivity to government agencies but also to sponsor programs aimed at removing the causes of societal discontent.
A New Approach to the Provision of Communications
-
The approach used differs from conventional communications, Conventional communications places significant power into the portable transceiver. The distance between transceivers is usually considerable, The WiFi topology is based on having many, many access points proximate to the users such that the portable device does not have to be very powerful and the transmissions are actually, deliberately limited in their range. This is very similar to the approach used with mobile phones, The WiFi towers consist of a WiFi transceiver and a router capable of providing local access to the WiFi transceiver and capable of performing the task of network address translation, In such an arrangement the actual potential bandwidth is the sum of all of the available paths that message can travel along to reach their destination, Such a network is also very hard to completely disable,
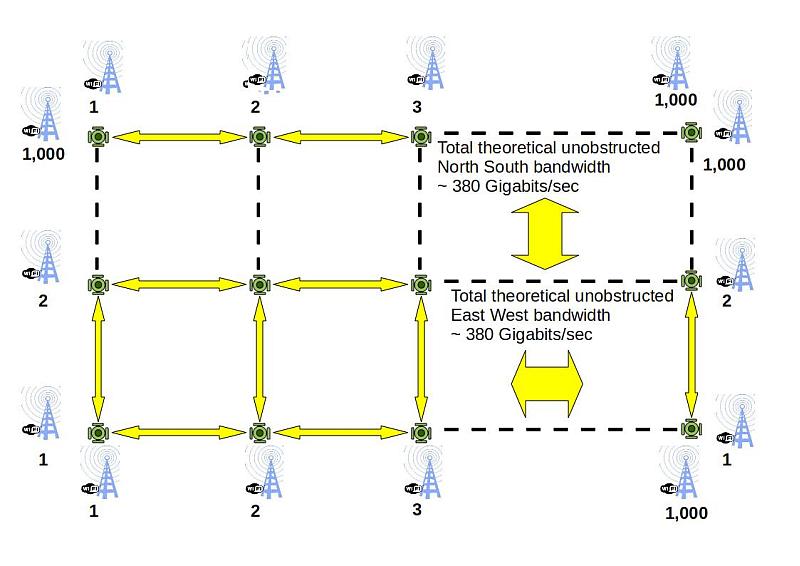
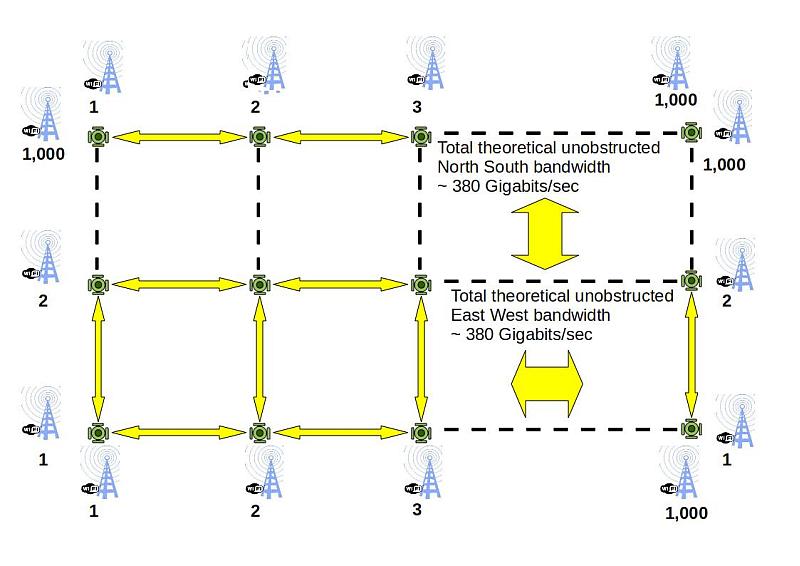
Figure 1. Theoretical East-West, North-South capacity of a Grid
-
Figure 1 provides an illustration of the power of a grid type networking arrangement, If the grid consists of 1,000 by 1,000 nodes and each line of communications has a bandwidth of 380 Megabits/sec the total bandwidth in the horizontal and vertical directions is 380 Gigabits/sec, In reality, these bandwidths are not achievable because traffic does not normally travel in a single axis, Nevertheless the power of a meshed grid is formidable, It should also be appreciated that much of the detailed traffic is local and so does not actually go across the grid for any distance.
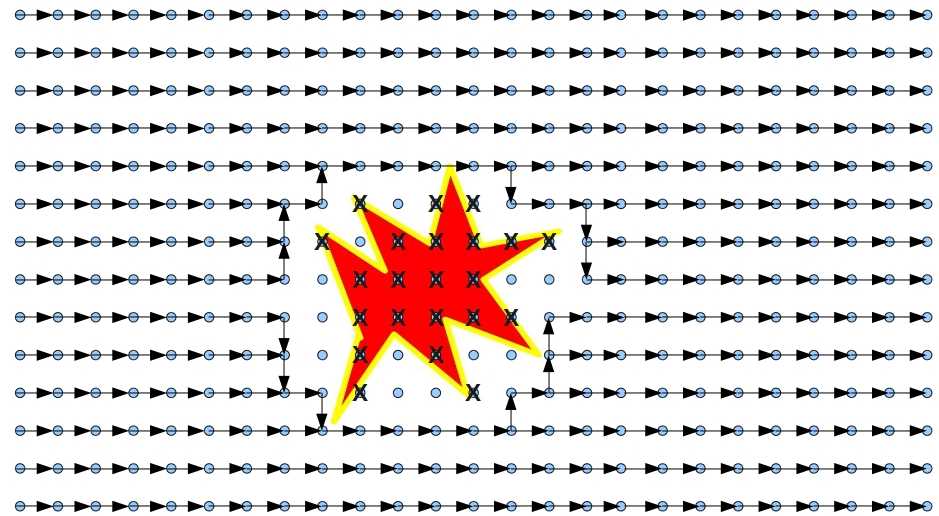
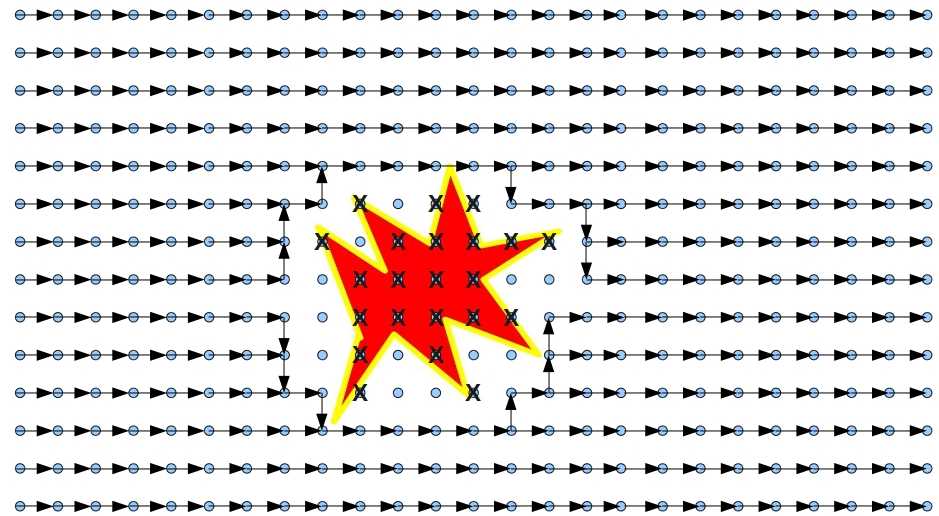
Figure 2. Meshed grid highly resistant to damage
-
Figure 2 provides an illustration of how a meshed grid is highly resistant to damage, With an intelligent routing system, the load is spread, as much as possible evenly across the network transceivers so as to maximise the available bandwidth for all users, The signalling to achieve this load sharing is, however, an overhead that will diminish the bandwidth of the total system, The more extensive and more intelligent the router signalling system, the greater is this overhead, There is a need then for optimisation of this network by communications engineers for any given set of circumstances, Even in its crudest form, however, this type of network offers far superior performance to the conventional systems that involve nesting and trunking of communications.
Implementation - Topology and Possible Hardware Solutions
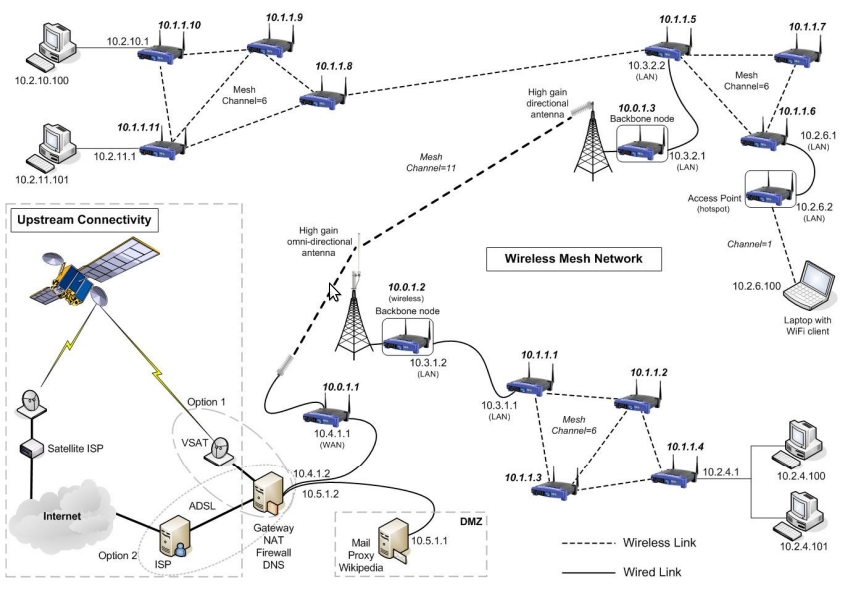
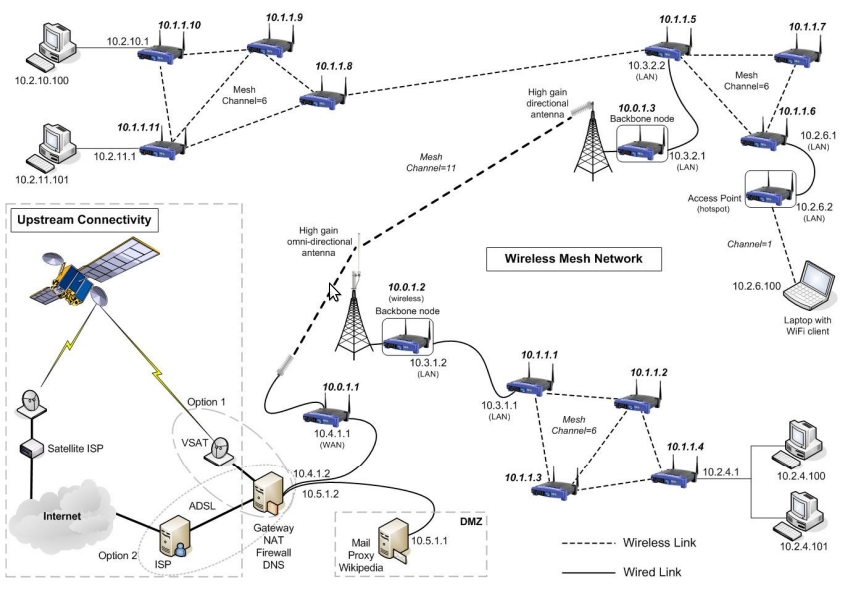
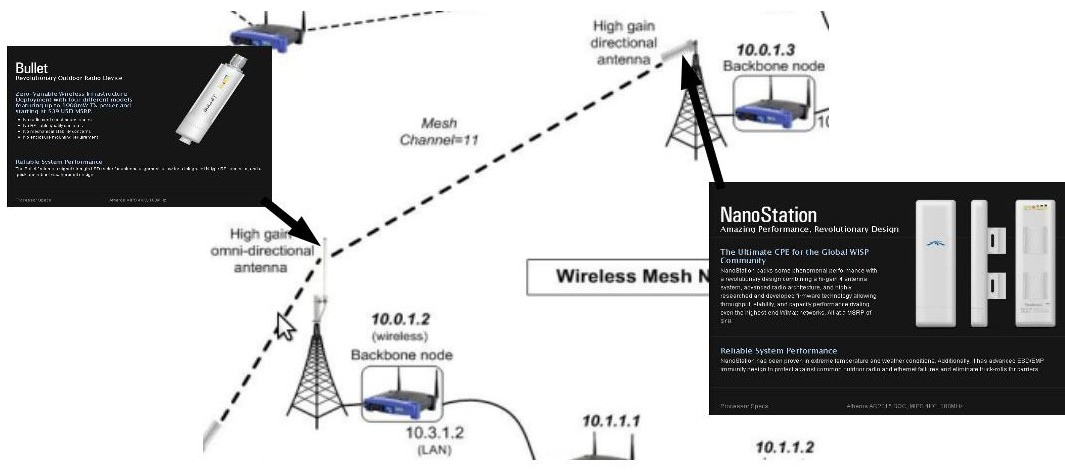
Figure 3. Example of a meshed WiFi Network

Figure 4. Bullet Antenna in low cost protective PVC downpipe
- Figure 3 provides an illustration of the topology that is possible at comparatively low cost, Figure 4 shows a WiFi antenna encapsulated in a low cost 60mm PVC tube attached to the outside of a building, A mast similar to this could be made of sections that slip together and can then be clamped to a vehicle, when the vehicle is stationary, to provide WiFi comms to a temporary base in the field.
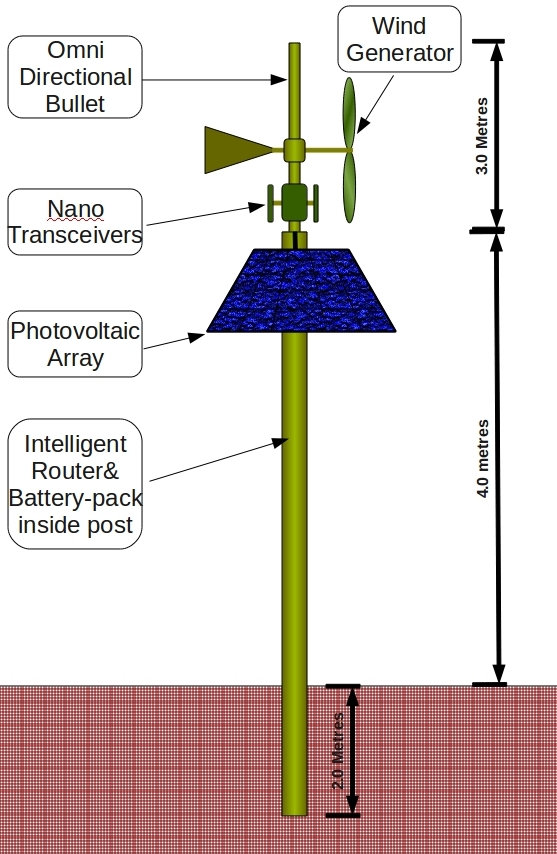
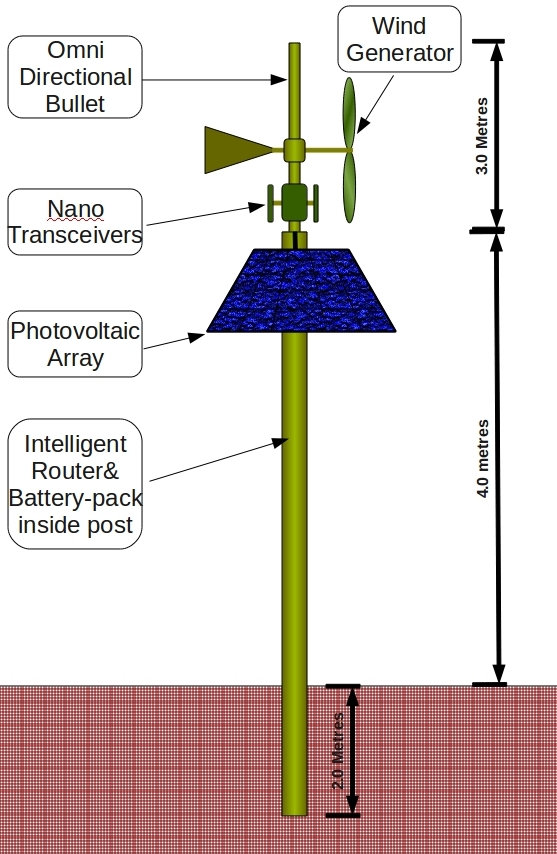
Figure 5. Example of a “Standard” Self Sustaining Communications Pole
- Figure 5 provides an illustration of a self sustaining communications pole. On it is mounted the WiFi antenna, 60 Watt Solar cell (around AUD $200.00) and a small wind turbine, Enclosed within the pole is an intelligent router and battery pack to support the operation of the pole when the sun is not shining and there is no wind, The pole is buried into the ground to a depth of 2 metres and surrounded by quick setting concrete delivered as a pre-mix in a bag.

Figure 6. Rapid boring of holes into dirt
- Figure 6 provides an illustration of an augur attached to the back end of a tractor, This borer is capable of boring a 2 metre hole in medium density dirt in around 10 minutes, The harder the ground, the shallower may be the drilling to result in a stable pole, It is estimated a communications pole can be installed in 15 minutes by a team of three people.
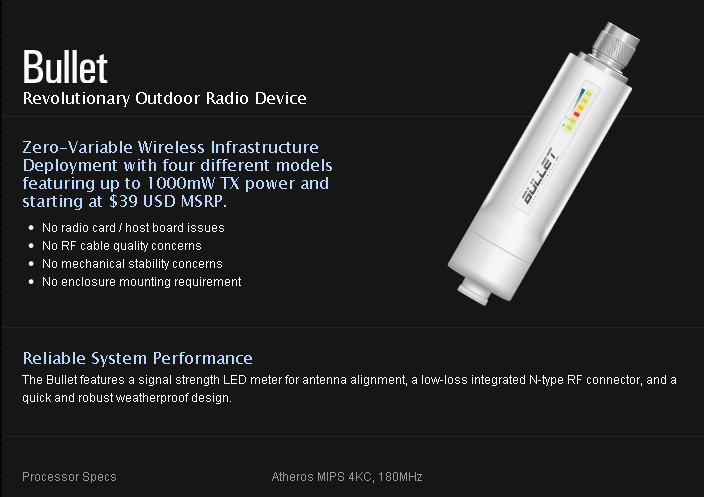
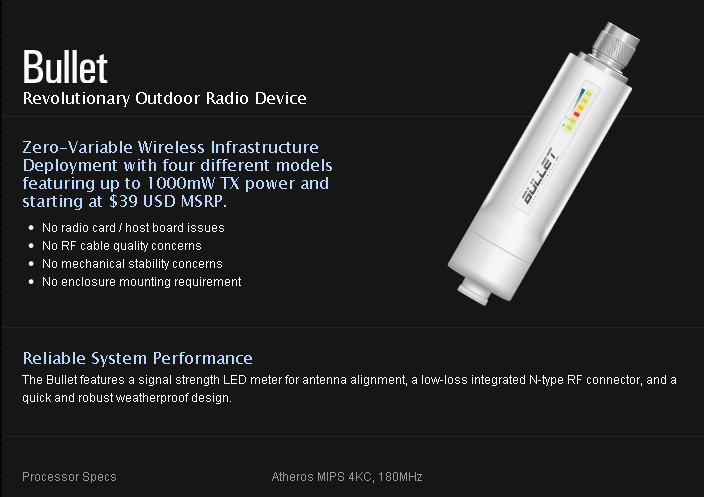
Figure 7. The Bullet - It sits at the base of the Antenna
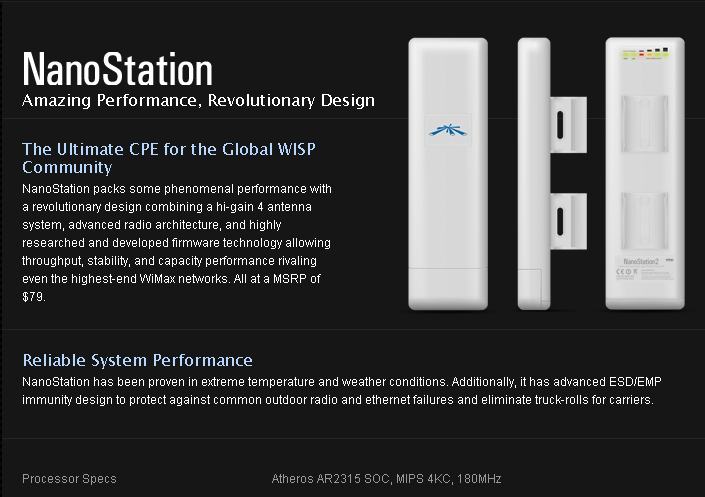
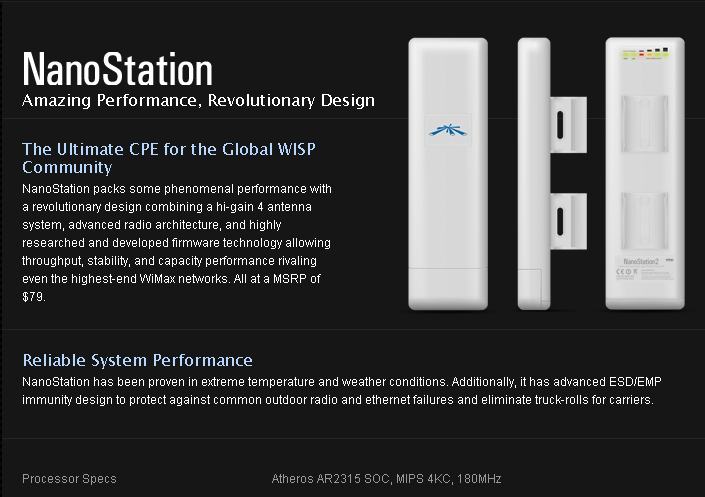
Figure 8. Two Nanos facing each other can communicate over a number of kilometres.
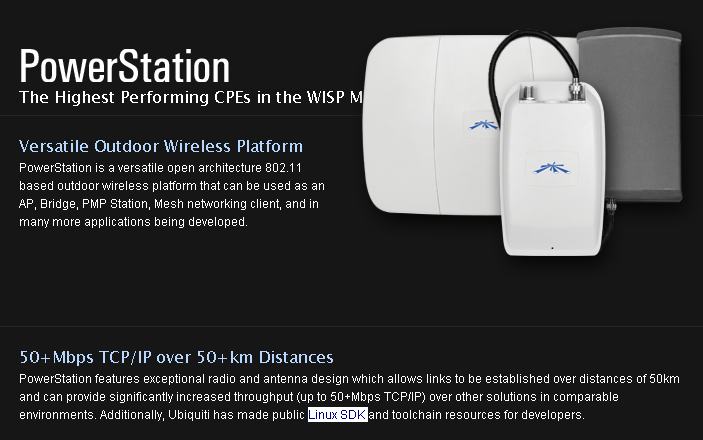
Figure 9. Power stations provide a link of approx 50km
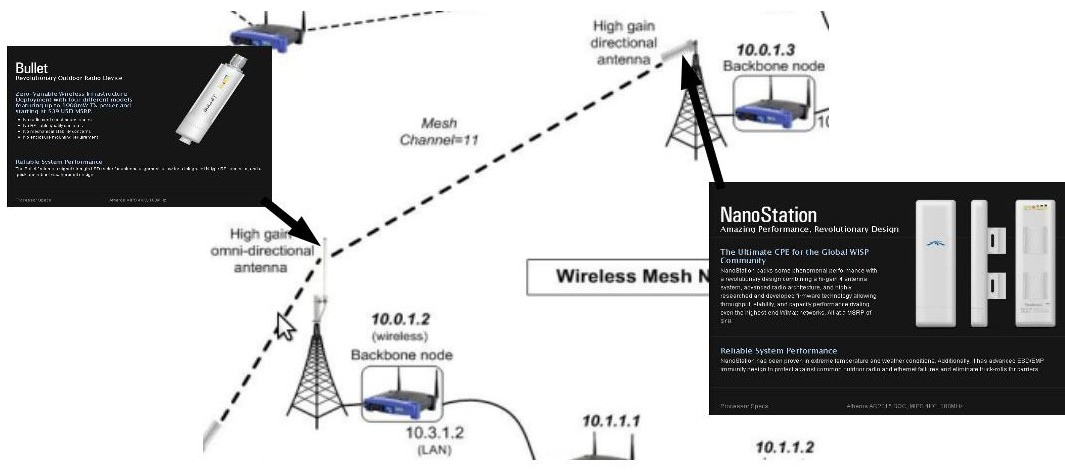
Figure 10. Example of the utilisation of the hardware depicted in this document
- The following figures 7, 8, and 9 provide examples of the hardware that has now been successfully trialled, Figure 10 provides further illustration of where these components fit in the scheme of things.
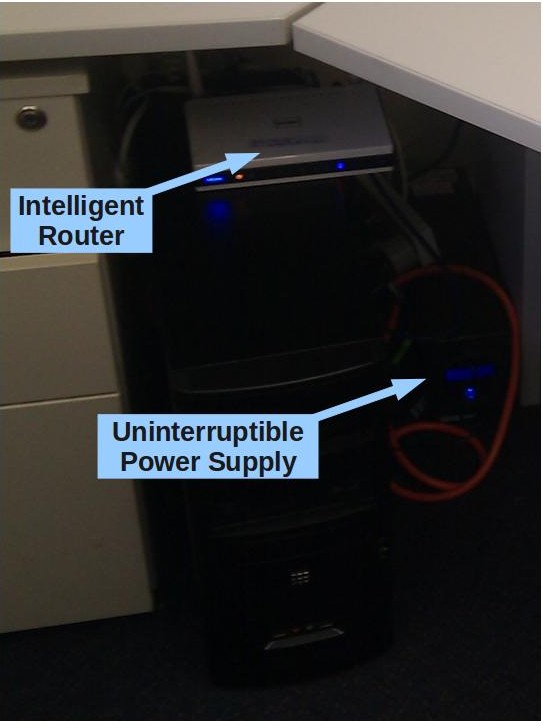
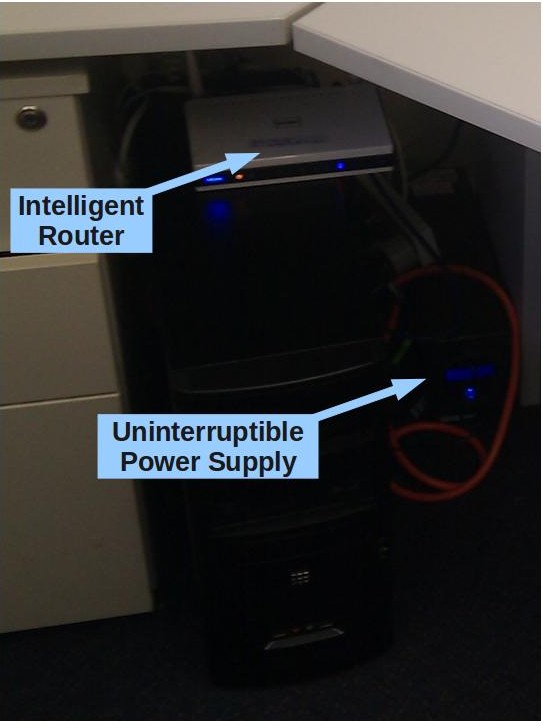
Figure 11. Intelligent Router setup - Cost $100.00
- Figure 11 provides an example of the set-up in an office, The Intelligent Router is of particular interest, It cost around AUD $100.00 and has sufficient memory to hold the Linux Operating System, It also has a USB interface so it is possible to connect it to a 1 Terabyte USB portable hard drive or to a USB hub such that it can then drive a number of USB devices, including a common commercial USB mobile broadband modem.
- Using this arrangement it is possible to have the router act in a number of roles, for example, as a mail or proxy server, Importantly the router only consumes around 12 to 15 Watts of power, The Ubiquiti Networks Inc., “Bullet” and “NanoStation” systems illustrated in this Annex also have low power requirements such that it may be possible to drive the complete assembly with a photovoltaic cell, wind-generator and backup battery pack arrangement; making it ideal for deployment into the field in remote areas, The exact cost of this arrangement needs to be ascertained by firstly building a complete assembly and then performing a market survey and engineering optimisation study to determine where parts and manufacturing could be obtained at the lowest possible price whilst maintaining a high quality standard.

Figure 12. Example of a low-cost, low-power server system.
- Figure 12 provides an experimental setup using a Marvell “Kirkwood 6281A1”, fitted with a dual core ARM processor based device, The two cores run at 1.2 GHz, The Kirkwood is equipped with 512 MB of DDR2 dynamic RAM and 512MB of flash memory, The box consumes 20 Watts of power and comes equipped with its own 54 Mbit WiFi (802.11g) transceiver, This design is customisable, Marvell will perform special production runs provided the number required exceeds 2,000 units, It would be possible to have multiple WiFi transceivers and to have them providing 380 Mbit/sec bandwidth (802.11n) if desired, The cost of the Marvell box was a little over $100 US, Attached to the box by USB are two 2.5” hard drives; each of 1Terabyte capacity providing a RAID 12 configuration.
- Further work has been performed experimenting with WiFi devices that have a bandwidth of 380 Megabits per second, This system of communication is extremely cheap and very safe; both from the point of emission and communications security.